Ransomware infections have been infecting computer systems for years now. From single users to entire enterprises, systems have been infiltrated and data held for a large amount of crypto currency. Once infected, the malware begins to encrypt your information and then will present a message to pay a ransom fee to recover your information.
How do you get infected?
The number one way for ransomware to make its way on to a computer system is by way of an email with a link or attachment that redirects the user to download “something” of value (eg a .PDf file or a Word Document).
How can you prevent a ransomware attack?
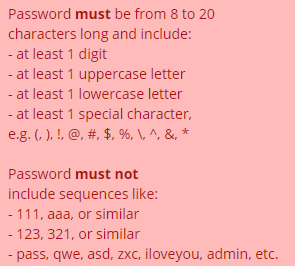
Although there is no way to completely prevent an infection, we recommend making sure that your computer has all of Windows updates installed and has proper, paid antivirus in place with the latest virus definition and program updates installed.
Keep an eye out for suspicious emails, even from those who you know. DO NOT open any emails that contain links or attachments that you are not familiar with.
What do you do after an attack?
If you do find yourself in a predicament where it is too late, shut down your computer immediately and reach out for help. Data can often be salvaged before the infection spreads and encrypts your data, but only if the computer is powered off before the infection spreads.
We recommend against paying the ransom in any scenario.
If the infection is caught before it spreads, data can often be extracted. If an infection does encrypt your data and holds it for ransom, restoring your data from backup is the best method of recovery. Paying the ransom fee rarely gets your information back from the attacker.
Warn other users!
A thorough investigation of the source of infection should be conducted to determine where the vulnerability was let in. Other users should be warned and cyber-security appliances, services, and subscriptions should be checked and tested.